Token Expired
Google APIs use the OAuth 2.0 protocol for authentication and say-so. Google supports common OAuth ii.0 scenarios such as those for web server, client-side, installed, and express-input device applications.
To brainstorm, obtain OAuth 2.0 client credentials from the Google API Console. So your client awarding requests an access token from the Google Authorization Server, extracts a token from the response, and sends the token to the Google API that you lot want to access. For an interactive demonstration of using OAuth 2.0 with Google (including the pick to use your ain client credentials), experiment with the OAuth 2.0 Playground.
This page gives an overview of the OAuth 2.0 authorization scenarios that Google supports, and provides links to more detailed content. For details nigh using OAuth 2.0 for hallmark, see OpenID Connect.
Basic steps
All applications follow a basic pattern when accessing a Google API using OAuth 2.0. At a high level, y'all follow v steps:
i. Obtain OAuth 2.0 credentials from the Google API Console.
Visit the Google API Console to obtain OAuth ii.0 credentials such every bit a customer ID and client secret that are known to both Google and your application. The gear up of values varies based on what blazon of application you are building. For example, a JavaScript application does not require a clandestine, merely a web server application does.
Before your application tin can admission individual data using a Google API, it must obtain an access token that grants access to that API. A single access token tin can grant varying degrees of access to multiple APIs. A variable parameter called scope controls the ready of resources and operations that an access token permits. During the access-token request, your application sends one or more than values in the scope parameter.
There are several ways to brand this request, and they vary based on the type of application you are building. For instance, a JavaScript application might request an access token using a browser redirect to Google, while an application installed on a device that has no browser uses web service requests.
Some requests require an authentication step where the user logs in with their Google account. Later on logging in, the user is asked whether they are willing to grant one or more permissions that your application is requesting. This procedure is called user consent.
If the user grants at to the lowest degree one permission, the Google Dominance Server sends your application an access token (or an authorisation code that your application can utilise to obtain an admission token) and a list of scopes of access granted by that token. If the user does not grant the permission, the server returns an error.
Information technology is more often than not a all-time practice to request scopes incrementally, at the time access is required, rather than up front. For case, an app that wants to support saving an event to a agenda should non request Google Calendar admission until the user presses the "Add to Calendar" button; see Incremental authorization.
3. Examine scopes of access granted past the user.
Compare the scopes included in the access token response to the scopes required to access features and functionality of your application dependent upon access to a related Google API. Disable whatever features of your app unable to part without admission to the related API.
The scope included in your request may non lucifer the scope included in your response, even if the user granted all requested scopes. Refer to the documentation for each Google API for the scopes required for access. An API may map multiple telescopic cord values to a single scope of access, returning the same telescopic string for all values allowed in the request. Example: the Google People API may render a scope of https://www.googleapis.com/auth/contacts when an app requested a user authorize a telescopic of https://world wide web.google.com/m8/feeds/; the Google People API method people.updateContact requires a granted telescopic of https://world wide web.googleapis.com/auth/contacts.
4. Transport the admission token to an API.
After an awarding obtains an access token, it sends the token to a Google API in an HTTP Authority request header. It is possible to send tokens every bit URI query-string parameters, simply we don't recommend it, considering URI parameters can end up in log files that are non completely secure. Likewise, information technology is adept Remainder do to avoid creating unnecessary URI parameter names.
Access tokens are valid only for the set of operations and resource described in the telescopic of the token asking. For example, if an admission token is issued for the Google Agenda API, information technology does not grant admission to the Google Contacts API. Y'all can, however, send that admission token to the Google Calendar API multiple times for similar operations.
5. Refresh the access token, if necessary.
Access tokens have limited lifetimes. If your application needs access to a Google API across the lifetime of a single admission token, it tin can obtain a refresh token. A refresh token allows your application to obtain new access tokens.
Scenarios
Spider web server applications
The Google OAuth 2.0 endpoint supports web server applications that use languages and frameworks such every bit PHP, Java, Python, Ruby, and ASP.Internet.
The authorization sequence begins when your application redirects a browser to a Google URL; the URL includes query parameters that indicate the type of admission beingness requested. Google handles the user hallmark, session selection, and user consent. The upshot is an authority lawmaking, which the awarding tin commutation for an access token and a refresh token.
The application should store the refresh token for future use and utilize the access token to access a Google API. Once the access token expires, the awarding uses the refresh token to obtain a new 1.
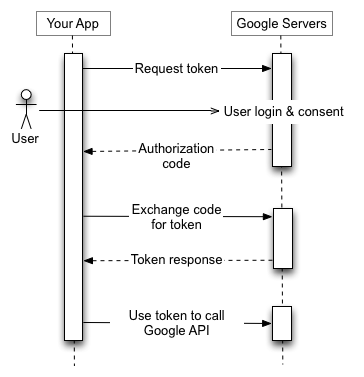
For details, run across Using OAuth 2.0 for Spider web Server Applications.
Installed applications
The Google OAuth 2.0 endpoint supports applications that are installed on devices such equally computers, mobile devices, and tablets. When you lot create a client ID through the Google API Panel, specify that this is an Installed application, so select Android, Chrome app, iOS, Universal Windows Platform (UWP), or Desktop app as the application type.
The procedure results in a client ID and, in some cases, a client secret, which yous embed in the source code of your application. (In this context, the client secret is obviously not treated every bit a secret.)
The authorization sequence begins when your application redirects a browser to a Google URL; the URL includes query parameters that indicate the type of admission being requested. Google handles the user authentication, session option, and user consent. The event is an authorisation code, which the application can substitution for an access token and a refresh token.
The application should store the refresh token for time to come use and utilize the access token to access a Google API. Once the access token expires, the application uses the refresh token to obtain a new one.
For details, see Using OAuth 2.0 for Installed Applications.
Client-side (JavaScript) applications
The Google OAuth 2.0 endpoint supports JavaScript applications that run in a browser.
The authorization sequence begins when your awarding redirects a browser to a Google URL; the URL includes query parameters that indicate the type of admission being requested. Google handles the user authentication, session choice, and user consent.
The outcome is an access token, which the client should validate before including it in a Google API request. When the token expires, the application repeats the procedure.
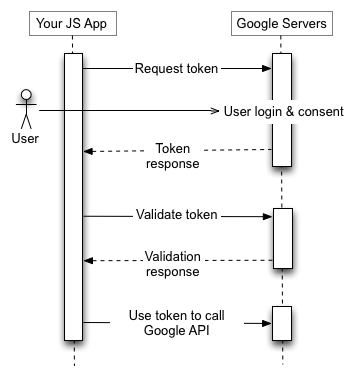
For details, run across Using OAuth 2.0 for Client-side Applications.
Applications on limited-input devices
The Google OAuth two.0 endpoint supports applications that run on limited-input devices such every bit game consoles, video cameras, and printers.
The authorization sequence begins with the application making a web service request to a Google URL for an authorization lawmaking. The response contains several parameters, including a URL and a lawmaking that the application shows to the user.
The user obtains the URL and lawmaking from the device, and then switches to a separate device or figurer with richer input capabilities. The user launches a browser, navigates to the specified URL, logs in, and enters the code.
Meanwhile, the application polls a Google URL at a specified interval. After the user approves access, the response from the Google server contains an access token and refresh token. The application should store the refresh token for future use and utilise the access token to access a Google API. Once the access token expires, the awarding uses the refresh token to obtain a new one.
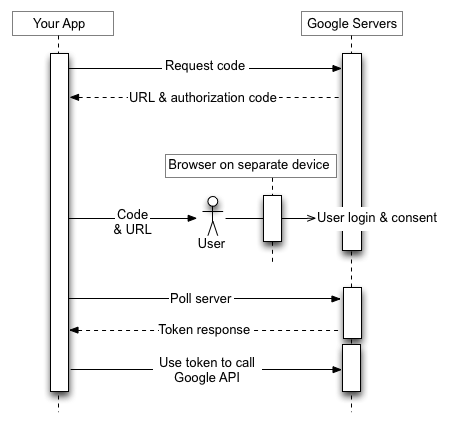
For details, meet Using OAuth ii.0 for Devices.
Service accounts
Google APIs such as the Prediction API and Google Cloud Storage tin human action on behalf of your application without accessing user information. In these situations your awarding needs to testify its own identity to the API, but no user consent is necessary. Similarly, in enterprise scenarios, your application can request delegated admission to some resources.
For these types of server-to-server interactions you need a service account, which is an business relationship that belongs to your application instead of to an individual end-user. Your awarding calls Google APIs on behalf of the service business relationship, and user consent is not required. (In not-service-account scenarios, your application calls Google APIs on behalf of end-users, and user consent is sometimes required.)
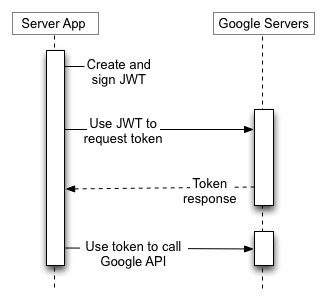
A service account'south credentials, which you obtain from the Google API Console, include a generated email accost that is unique, a client ID, and at to the lowest degree 1 public/private key pair. Y'all employ the customer ID and one individual primal to create a signed JWT and construct an access-token asking in the advisable format. Your application then sends the token request to the Google OAuth two.0 Authorization Server, which returns an access token. The application uses the token to access a Google API. When the token expires, the application repeats the procedure.
For details, see the service-account documentation.
Token size
Tokens can vary in size, upwardly to the following limits:
- Authorization codes: 256 bytes
- Access tokens: 2048 bytes
- Refresh tokens: 512 bytes
Admission tokens returned by Google Deject's Security Token Service API are structured similarly to Google API OAuth 2.0 access tokens merely have different token size limits. For details, see the API documentation.
Google reserves the correct to change token size within these limits, and your application must back up variable token sizes accordingly.
Refresh token expiration
You must write your lawmaking to conceptualize the possibility that a granted refresh token might no longer piece of work. A refresh token might stop working for ane of these reasons:
- The user has revoked your app'south access.
- The refresh token has not been used for half dozen months.
- The user changed passwords and the refresh token contains Gmail scopes.
- The user account has exceeded a maximum number of granted (live) refresh tokens.
- The user belongs to a Google Deject Platform organization that has session control policies in effect.
A Google Cloud Platform project with an OAuth consent screen configured for an external user type and a publishing status of "Testing" is issued a refresh token expiring in seven days.
There is currently a limit of 50 refresh tokens per Google Account per OAuth two.0 client ID. If the limit is reached, creating a new refresh token automatically invalidates the oldest refresh token without warning. This limit does non utilize to service accounts.
There is also a larger limit on the total number of refresh tokens a user account or service business relationship can have across all clients. Most normal users won't exceed this limit but a developer's business relationship used to test an implementation might.
If yous need to authorize multiple programs, machines, or devices, 1 workaround is to limit the number of clients that y'all authorize per Google Account to 15 or 20. If you are a Google Workspace admin, y'all can create boosted users with administrative privileges and use them to authorize some of the clients.
Dealing with session control policies for Google Deject Platform (GCP) organizations
Administrators of GCP organizations might require frequent reauthentication of users while they admission GCP resources, using the Google Cloud session control characteristic. This policy impacts admission to Google Cloud Panel, the Google Cloud SDK (as well known as the gcloud CLI), and any third party OAuth application that requires the Deject Platform scope. If a user has a session command policy in place then on the expiry of the session duration, your API calls volition error out similar to what would happen if the refresh token was revoked - the call volition fail with an error type invalid_token; the sub-mistake type tin can be used to distinguish between a revoke token and a failure due to a session control policy. As session durations can exist very limited (between i hour to 24 hours), this scenario must be handled gracefully by restarting an auth session.
Every bit, you must not use, or encourage the use of, user credentials for server to server deployment. If user credentials are deployed on a server for long running jobs or operations and a customer applies session control policies on such users, the server application will fail as there volition exist no style to re-authenticate the user when the session elapsing expires.
For more than information on how to help your customers deploy this feature, refer to this admin-focussed help article.
Customer libraries
The following client libraries integrate with pop frameworks, which makes implementing OAuth two.0 simpler. More features will be added to the libraries over time.
- Google API Client Library for Coffee
- Google API Customer Library for Python
- Google API Customer Library for Go
- Google API Customer Library for .Net
- Google API Client Library for Ruby
- Google API Client Library for PHP
- Google API Client Library for JavaScript
- GTMAppAuth - OAuth Customer Library for Mac and iOS
Source: https://developers.google.com/identity/protocols/oauth2
0 Response to "Token Expired"
Post a Comment